2022-11-06 319
下面是我的做法:
首先,配置系统盘下(如:c盘)的权限(已经将IIS的默认文件夹删除)
1.系统盘:选中系统盘,属性,安全选项卡,删掉除了administrators和system组的其他组或者用户。
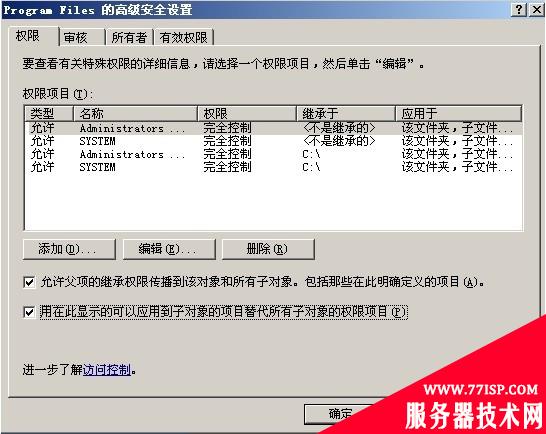
2.Program Files :右键文件夹->选择属性->选择“安全”选项卡->点击“高级”选项->选中“允许父项…”和“用在此显示…”->点击“复制”->点击确定,退出高级安全设置->把安全选项卡中除了administrators和system组之外的组或者用户删除
高级安全设置效果如下:
3.Program Files/Common File/users : 进入到program files下的common file文件夹下面,找到system添加users,默认的权限即可。所谓默认权限就是你添加这个用户系统自动授予这个用户对于操作文件夹或者文件的权限。(可能有人要问为什么要给这个文件夹设置users的权限?答:这个部分里面有一些dll文件是asp中createobject的时候需要的)
4.Documents and Settings:进入系统盘,选中Documents and Settings文件夹右键,删除掉除了administrator、system、power users组之外的其他用户或者组。进入到Documents and Settings文件夹里面,administrator这个文件夹的权限无需设置。ALL users文件夹,进入到高级选项选择“用在此显示的可以应用到子对象的目录替代所有子对象的权限项目”,确定,到安全选项卡下面删掉除了 administrator和system之外的其他用户组和用户,点击确定。Default users文件夹,进入到高级选项选择“用在此显示的可以应用到子对象的目录替代所有子对象的权限项目”,确定,到安全选项卡下面删掉除了 administrator、system、power users之外的其他用户组和用户,点击确定。
5.Windows : 右键文件夹->选择属性->选择“安全”选项卡->删除掉除了administrator和system之外的用户->点击确定。
6.Windows/temp : 右键文件夹->选择属性->选择“安全”选项卡->添加users组->设置users组只具有读取、写入的权限。
7.其他根目录下的文件夹:右键文件夹->选择属性->选择“安全”选项卡->点击“高级”选项->选中“允许父项…”和“用在此显示…”->点击“复制”->点击确定,退出高级安全设置->把“安全”选项卡中除了administrators和system组之外的组或者用户删除
8.批处理:接下来的是一些特殊文件夹、文件的权限,一些服务的修改,危险组件的删除。
批处理的部分最后附上下面的保存为*.bat或者直接从我提供的下载的地方下载即可。
@echo off
ECHO.
ECHO.
ECHO. ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
ECHo.
ECHo "windows2003NTFS加固脚本"
ECHo.
ECHO. ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
ECHO.
ECHO.
ECHO. -------------------------------------------------------------------------
ECHo 请按提示操作备份好注册表,否则修改后无法还原,本人不负责.
ECHO.
ECHO YES=next set NO=exit (this time 30 Second default for n)
ECHO. -------------------------------------------------------------------------
CHOICE /T 30 /C yn /D n
if errorlevel 2 goto end
if errorlevel 1 goto next
:next
if EXIST backup (echo.)else md backup
if EXIST temp (rmdir /s/q temp|md temp) else md temp
if EXIST backup\backupkey.reg (move backup\backupkey.reg backup\backupkey_old.reg ) else goto run
:run
regedit /e temp\backup-reg1.key1 "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\"
regedit /e temp\backup-reg2.key2 "HKEY_CLASSES_ROOT\"
copy /b /y /v temp\backup-reg1.key1+temp\backup-reg2.key2 backup\backupkey.reg
if exist backup\wshom.ocx (echo 备份已存在) else copy /v/y %SystemRoot%\System32\wshom.ocx backup\wshom.ocx
if exist backup\shell32.dll (echo 备份已存在) else copy /v/y %SystemRoot%\system32\shell32.dll backup\shell32.dll
ECHO 备份已经完成
ECHO.
goto next2
:next2
ECHO.
ECHO. -------------------------------------------------------------------
ECHo 修改权限system32目录中不安全的几个exe文件,改为只有Administrators才有权限运行
ECHO YES=next set NO=this set ignore (this time 30 Second default for y)
ECHO. -------------------------------------------------------------------
CHOICE /T 30 /C yn /D y
if errorlevel 2 goto next3
if errorlevel 1 goto next21
:next21
echo y|cacls.exe %SystemRoot%\system32\net.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\net1.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\cmd.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\tftp.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\netstat.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\regedit.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\at.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\attrib.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\cacls.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\fortmat.com /g Administrators:F
echo y|cacls.exe %SystemDrive%\boot.ini /g Administrators:F
echo y|cacls.exe %SystemDrive%\AUTOEXEC.BAT /g Administrators:F
echo y|cacls.exe %SystemRoot%/system32\ftp.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\secedit.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\gpresult.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\gpupdate.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\logoff.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\shutdown.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\telnet.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\wscript.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\doskey.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\help.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\ipconfig.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\nbtstat.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\print.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\debug.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\regedt32.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\reg.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\register.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\replace.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\nwscript.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\share.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\ping.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\ipsec6.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\netsh.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\edit.com /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\route.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\tracert.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\powercfg.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\nslookup.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\arp.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\rsh.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\netdde.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\mshta.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\mountvol.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\setx.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\find.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\where.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\finger.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\regsvr32.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\sc.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\shadow.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\runas.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\PCHealth\HelpCtr\Binaries\msconfig.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\notepad.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\regedit.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\winhelp.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\winhlp32.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\edlin.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\posix.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\atsvc.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\qbasic.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\runonce.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\syskey.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\cscript.exe /g Administrators:F
echo y|cacls.exe %SystemRoot%\system32\sethc.exe /g Administrators:F
echo "C盘权限设定"
cacls "%SystemRoot%/Registration" /r "everyone" /e
echo "删除C盘的windows目录下的create owner的权限"
cd/
cacls "%SystemRoot%/repair" /r "create owner" /e
cacls "%SystemRoot%/system32" /r "create owner" /e
cacls "%SystemDrive%/system32/config" /r "create owner" /e
cacls "%SystemRoot%/system32/wbem" /r "create owner" /e
echo "删除WINDOWS文件夹下面的power users的权限"
cacls "%SystemRoot%/repair" /r "Power Users" /e
cacls "%SystemRoot%/system32" /r "Power Users" /e
cacls "%SystemDrive%/system32/config" /r "Power Users" /e
cacls "%SystemRoot%/system32/wbem" /r "Power Users" /e
echo "删除WINDOWS下users的访问权限"
cacls "%SystemRoot%/addins" /r "users" /e
cacls "%SystemRoot%/AppPatch" /r "users" /e
cacls "%SystemRoot%/Connection Wizard" /r "users" /e
cacls "%SystemRoot%/Debug" /r "users" /e
cacls "%SystemRoot%/Driver Cache" /r "users" /e
cacls "%SystemRoot%/Help" /r "users" /e
cacls "%SystemRoot%/IIS Temporary Compressed Files" /r "users" /e
cacls "%SystemRoot%/java" /r "users" /e
cacls "%SystemRoot%/msagent" /r "users" /e
cacls "%SystemRoot%/mui" /r "users" /e
cacls "%SystemRoot%/repair" /r "users" /e
cacls "%SystemRoot%/Resources" /r "users" /e
cacls "%SystemRoot%/security" /r "users" /e
cacls "%SystemRoot%/system" /r "users" /e
cacls "%SystemRoot%/TAPI" /r "users" /e
cacls "%SystemRoot%/Temp" /r "users" /e
cacls "%SystemRoot%/twain_32" /r "users" /e
cacls "%SystemRoot%/Web" /r "users" /e
cacls "%SystemRoot%/system32/3com_dmi" /r "users" /e
cacls "%SystemRoot%/system32/administration" /r "users" /e
cacls "%SystemRoot%/system32/Cache" /r "users" /e
cacls "%SystemRoot%/system32/CatRoot2" /r "users" /e
cacls "%SystemRoot%/system32/Com" /r "users" /e
cacls "%SystemRoot%/system32/config" /r "users" /e
cacls "%SystemRoot%/system32/dhcp" /r "users" /e
cacls "%SystemRoot%/system32/drivers" /r "users" /e
cacls "%SystemRoot%/system32/export" /r "users" /e
cacls "%SystemRoot%/system32/icsxml" /r "users" /e
cacls "%SystemRoot%/system32/lls" /r "users" /e
cacls "%SystemRoot%/system32/LogFiles" /r "users" /e
cacls "%SystemRoot%/system32/MicrosoftPassport" /r "users" /e
cacls "%SystemRoot%/system32/mui" /r "users" /e
cacls "%SystemRoot%/system32/oobe" /r "users" /e
cacls "%SystemRoot%/system32/ShellExt" /r "users" /e
cacls "%SystemRoot%/system32/wbem" /r "users" /e
goto next3
:next3
ECHO.
ECHO.
ECHO. ------------------------------------------------------------------------
ECHo 禁止不必要的服务,如果要退出请按Ctrl+C
ECHO YES=next set NO=this set ignore (this time 30 Second default for y)
ECHO. ------------------------------------------------------------------------
CHOICE /T 30 /C yn /D y
if errorlevel 2 goto next4
if errorlevel 1 goto next31
:next31
echo Windows Registry Editor Version 5.00 >temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\lanmanworkstation] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Alerter] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Browser] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Dfs] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Scheduler] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\LmHosts] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\TlntSvr] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\RemoteAccess] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\NtmsSvc] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\RemoteRegistry] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\TrkWks] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\ERSvc] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Messenger] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\NetLogon] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\NetLogon] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\NetDDE] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\NetDDEdsdm] >>temp\Services.reg
echo "Start"=dword:00000004 >>temp\Services.reg
regedit /s temp\Services.reg
ECHO.
goto next4
:next4
ECHO.
ECHO. -------------------------------------------------------------------------
ECHo 防止人侵和攻击. 如果要退出请按Ctrl+C
ECHO YES=next set NO=this set ignore (this time 30 Second default for y)
ECHO. -------------------------------------------------------------------------
CHOICE /T 30 /C yn /D y
if errorlevel 2 goto next5
if errorlevel 1 goto next41
:next41
echo Windows Registry Editor Version 5.00 >temp\skyddos.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Tcpip\Parameters] >>temp\skyddos.reg
echo "EnableDeadGWDetect"=dword:00000000 >>temp\skyddos.reg
echo "EnableICMPRedirects"=dword:00000000 >>temp\skyddos.reg
echo "PerformRouterDiscovery"=dword:00000000 >>temp\skyddos.reg
echo "NoNameReleaseOnDemand"=dword:00000001 >>temp\skyddos.reg
echo "KeepAliveTime"=dword:000493e0 >>temp\skyddos.reg
echo "EnablePMTUDiscovery"=dword:00000000 >>temp\skyddos.reg
echo "SynAttackProtect"=dword:00000002 >>temp\skyddos.reg
echo "TcpMaxHalfOpen"=dword:00000064 >>temp\skyddos.reg
echo "TcpMaxHalfOpenRetried"=dword:00000050 >>temp\skyddos.reg
echo "TcpMaxConnectResponseRetransmissions"=dword:00000001 >>temp\skyddos.reg
echo "TcpMaxDataRetransmissions"=dword:00000003 >>temp\skyddos.reg
echo "TCPMaxPortsExhausted"=dword:00000005 >>temp\skyddos.reg
echo "DisableIPSourceRouting"=dword:0000002 >>temp\skyddos.reg
echo "TcpTimedWaitDelay"=dword:0000001e >>temp\skyddos.reg
echo "EnableSecurityFilters"=dword:00000001 >>temp\skyddos.reg
echo "TcpNumConnections"=dword:000007d0 >>temp\skyddos.reg
echo "TcpMaxSendFree"=dword:000007d0 >>temp\skyddos.reg
echo "IGMPLevel"=dword:00000000 >>temp\skyddos.reg
echo "DefaultTTL"=dword:00000016 >>temp\skyddos.reg
echo 删除IPC$(Internet Process Connection)是共享“命名管道”的资源
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa] >>temp\skyddos.reg
echo "restrictanonymous"=dword:00000001 >>temp\skyddos.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Tcpip\Parameters\Interfaces\interfaces] >>temp\skyddos.reg
echo "PerformRouterDiscovery"=dword:00000000 >>temp\skyddos.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\NetBT\Parameters] >>temp\skyddos.reg
echo "BacklogIncrement"=dword:00000003 >>temp\skyddos.reg
echo "MaxConnBackLog"=dword:000003e8 >>temp\skyddos.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Afd\Parameters] >>temp\skyddos.reg
echo "EnableDynamicBacklog"=dword:00000001 >>temp\skyddos.reg
echo "MinimumDynamicBacklog"=dword:00000014 >>temp\skyddos.reg
echo "MaximumDynamicBacklog"=dword:00002e20 >>temp\skyddos.reg
echo "DynamicBacklogGrowthDelta"=dword:0000000a >>temp\skyddos.reg
echo [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\lanmanserver\parameters] >>temp\skyddos.reg
echo "autoshareserver"=dword:00000000 >>temp\skyddos.reg
regedit /s temp\skyddos.reg
ECHO.
ECHO.
goto next5
:next5
ECHO.
ECHO. ------------------------------------------------------------------------
ECHo 防止ASP木马运行 卸除WScript.Shell, Shell.application, WScript.Network
ECHO YES=next set NO=this set ignore (this time 30 Second default for y)
ECHO. -----------------------------------------------------------------------
CHOICE /T 30 /C yn /D y
if errorlevel 2 goto next6
if errorlevel 1 goto next51
:next51
echo Windows Registry Editor Version 5.00 >temp\del.reg
echo [-HKEY_CLASSES_ROOT\Shell.Application] >>temp\del.reg
echo [-HKEY_CLASSES_ROOT\Shell.Application.1] >>temp\del.reg
echo [-HKEY_CLASSES_ROOT\CLSID\{13709620-C279-11CE-A49E-444553540000}] >>temp\del.reg
echo [-HKEY_CLASSES_ROOT\ADODB.Command\CLSID] >>temp\del.reg
echo [-HKEY_CLASSES_ROOT\CLSID\{00000566-0000-0010-8000-00AA006D2EA4}] >>temp\del.reg
regedit /s temp\del.reg
regsvr32 /u %SystemRoot%\system32\wshom.ocx
del /f/q %SystemRoot%\System32\wshom.ocx
regsvr32 /u %SystemRoot%\system32\shell32.dll
del /f/q %SystemRoot%\System32\shell32.dll
rmdir /q/s temp
ECHO.
goto next6
:next6
ECHO.
ECHO.
ECHO. ---------------------------------------------------------------------
ECHo 设置已经完成重启后才能生效.
ECHO YES=reboot server NO=exit (this time 60 Second default for y)
ECHO. ----------------------------------------------------------------------
CHOICE /T 30 /C yn /D y
if errorlevel 2 goto end
if errorlevel 1 goto reboot
:reboot
shutdown /r /t 0
:end
if EXIST temp (rmdir /s/q temp|exit) else exit原文链接:https://77isp.com/post/12128.html
=========================================
https://77isp.com/ 为 “云服务器技术网” 唯一官方服务平台,请勿相信其他任何渠道。
数据库技术 2022-03-28
网站技术 2023-01-07
网站技术 2022-11-26
网站技术 2022-11-17
Windows相关 2022-02-23
网站技术 2023-01-14
Windows相关 2022-02-16
Windows相关 2022-02-16
Linux相关 2022-02-27
数据库技术 2022-02-20
小游客游戏攻略网游戏攻略网 2024年07月26日
抠敌 2023年10月23日
嚼餐 2023年10月23日
男忌 2023年10月22日
瓮仆 2023年10月22日
扫码二维码
获取最新动态
